A massive malware campaign known as “StealTok” involves at least 12 interrelated browser extensions. These extensions masquerade as TikTok video downloaders but secretly track user activity and harvest sensitive data.
The campaign uncovered by LayerX security has affected over 130,000 users worldwide, with approximately 12,500 installations still active across the Google Chrome and Microsoft Edge marketplaces.
The attackers use a highly organized approach, releasing multiple clones or slightly rebranded versions of the same core extension.
This creates a resilient operation: when one extension is identified and removed, threat actors upload a new clone to replace it.
To gain user trust, the malicious extensions initially function perfectly as advertised, allowing users to download TikTok videos without watermarks.
Many of these tools even earned a “Featured” badge in official extension stores, significantly reducing user suspicion and boosting download numbers.
What makes this campaign particularly dangerous is its use of delayed capability injection.

For the first 6 to 12 months, the extensions behave legitimately, building a solid reputation and passing initial security reviews.
Once enough time has passed, the extensions connect to external command-and-control servers to download dynamic remote configurations.
This hidden mechanism allows the attackers to fundamentally alter the extension’s behavior, turning a harmless video downloader into a powerful spyware tool without alerting the user or the marketplace.
After the malicious features are activated, the extensions begin quietly gathering extensive telemetry on the user.
They monitor usage patterns, track downloaded content, and collect high-entropy data, such as time zone, language settings, and even device battery status.
By combining these specific data points, the attackers can create a highly accurate “fingerprint” of the user’s device, enabling them to track the user across different web sessions and services.
To hide this data theft, the extensions send the information to deceptive domains with misspelled names, like “trafficreqort.com,” to avoid casual detection.
This campaign highlights a critical weakness in current browser security: relying solely on installation-time validation is no longer enough.
Because these extensions use remote configurations to evolve, the real risk happens long after the initial download.
Security experts recommend that organizations adopt continuous, behavior-based monitoring to detect suspicious network activity, hidden data collection, and unexpected permission usage in real-time.
Active and Removed Threats
LayerX security researchers identified several specific extensions involved in the StealTok campaign.
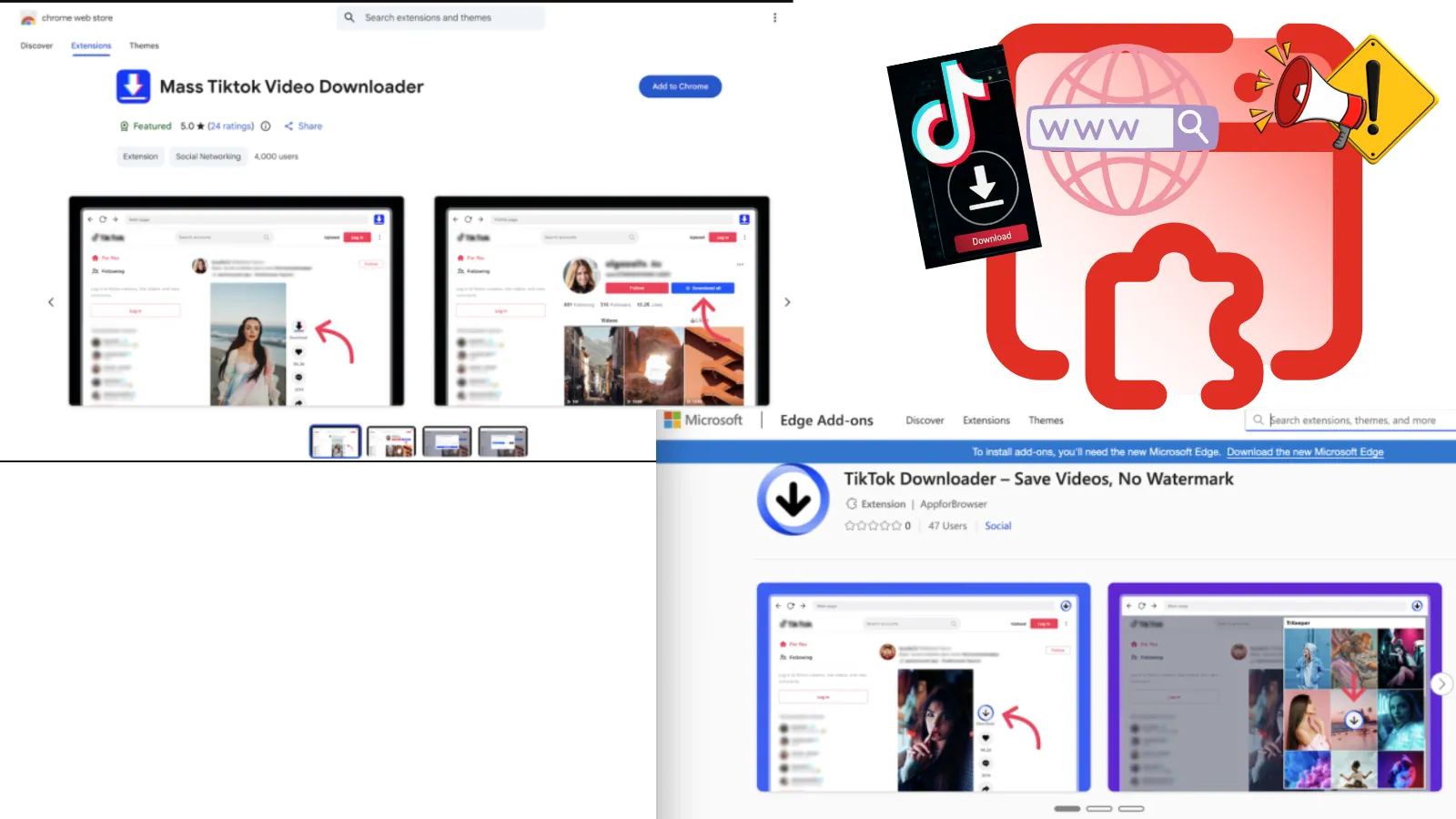
On Google Chrome, active threats include “TikTok Downloader – Save Videos, No Watermark” with 3,000 installs, “TikTok Video Downloader – Bulk Save” with 1,000 installs, and “Tiktok Downloader” with 353 installs.
On Microsoft Edge, active malicious extensions include “Mass Tiktok Video Downloader” with 77 installs and another version named “TikTok Downloader – Save Videos, No Watermark” with 47 installs.
Several highly popular versions of this malware have already been removed from Google Chrome, including “TikTok Video Keeper,” which had reached 60,000 installs, and “Video Downloader for Tiktok,” which had 20,000 installs.
If you have any of these extensions installed, security experts advise removing them immediately and changing passwords for sensitive accounts.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.